The Women of Seamfix – Stories . Growth . Impact
What’s it actually like working at Seamfix as a woman? This Women’s Month, we asked a few of the women across our teams to share
Business insights and articles written by our team of world-class professionals
What’s it actually like working at Seamfix as a woman? This Women’s Month, we asked a few of the women across our teams to share

Nigeria’s NIN-SIM linkage policy has become one of the most consequential regulatory mandates for telecom operators in recent years. Driven by the need to strengthen
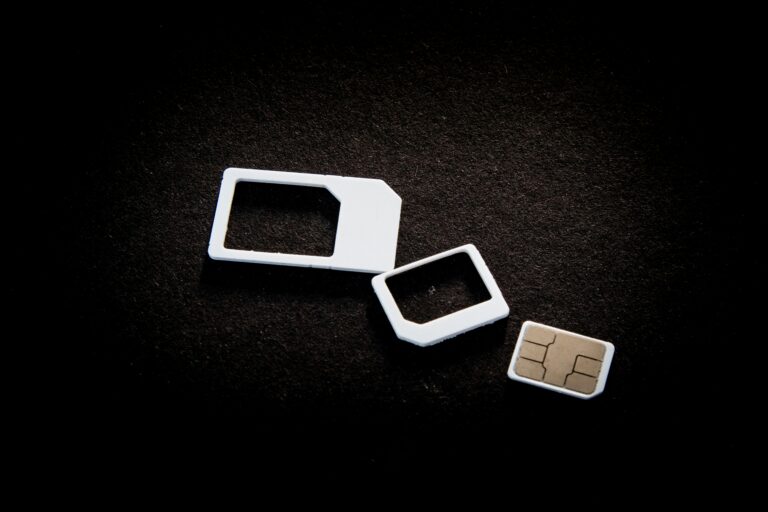
A customer walks into a telecom outlet to register a SIM card. The agent reaches for a paper form, asks a few questions, and carefully

In 2023, a Tier-1 telecom operator in Africa ran a nationwide compliance audit. On paper, everything looked fine. Millions of SIMs had been registered. KYC
A few years ago, SIM registration was treated as a routine requirement. Telcos collected customer information, stored it, and moved on. Compliance was important,
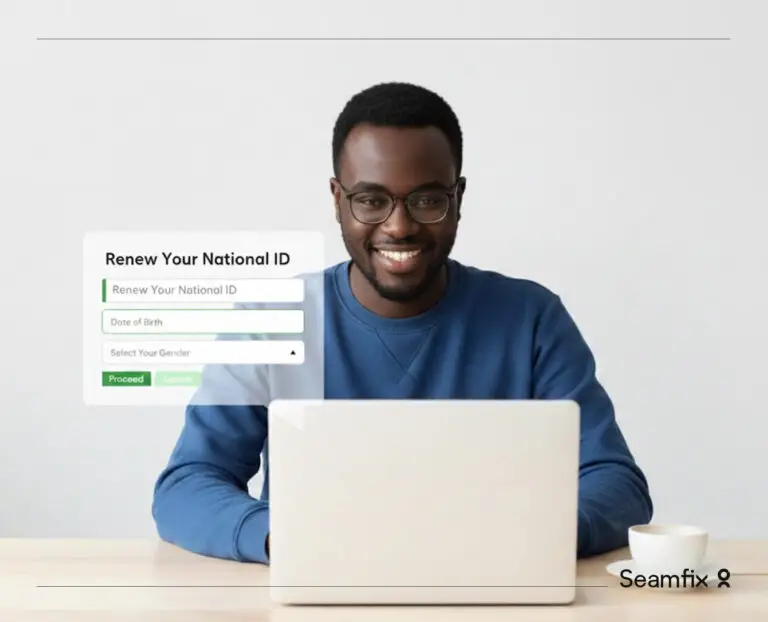
Governments do not fail citizens because they lack intent. They fail when systems cannot answer a basic question. Who is this person and what are

The problem growth exposes A fast growing company hires fifty people in three months and gives new staff shared passwords so work can start on
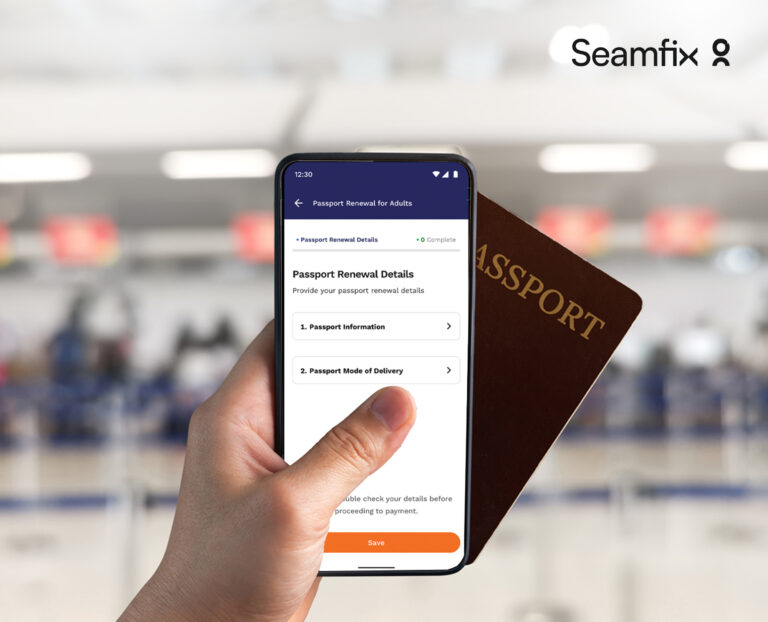
For millions of citizens living outside their home countries, renewing an international passport can be stressful, expensive, and time-consuming. Long journeys to embassies, extended waiting

Africa is moving money faster than ever, but many institutions still struggle with the same question: how do you keep payments quick while keeping them