
Dynamic access provisioning: Benefits and examples.
Ever feel like managing who gets access to what at work is like playing a never-ending game of “Simon Says”? Traditional access control methods can
Business insights and articles written by our team of world-class professionals

Ever feel like managing who gets access to what at work is like playing a never-ending game of “Simon Says”? Traditional access control methods can

Imagine running a ship. You’ve got a crew of talented people, each with their own roles and responsibilities. But what happens when someone new joins
Imagine this: You’re hosting a party, and instead of giving everyone a key to your house, you only hand out keys to the people who
Adaptive Authentication in IAM Let’s talk about security for a minute. We all know it’s important, but let’s be honest—it can also be a hassle.
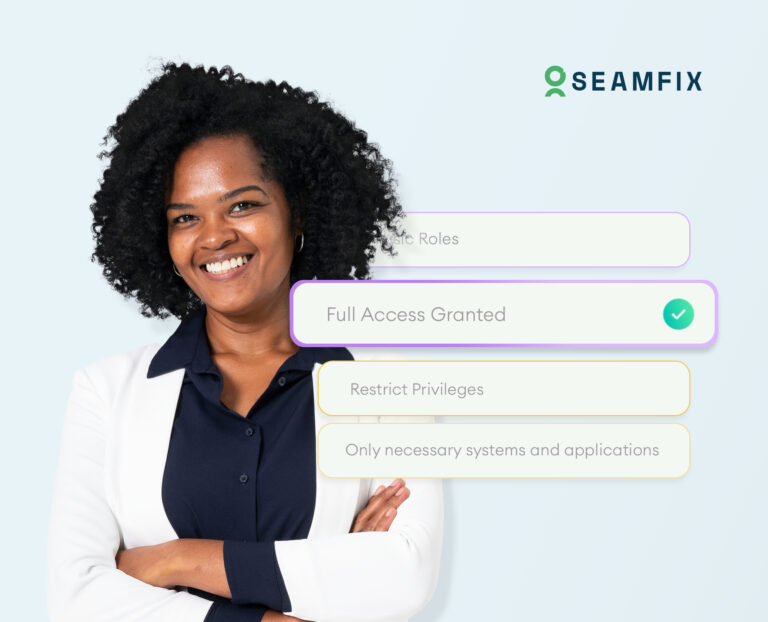
Imagine you’re handing out keys to your house. You wouldn’t give a spare key to every single person you know, right? Instead, you’d give keys
Role Based vs. Attribute Based vs. Policy Based Access Control Imagine you’re running a theme park. You’ve got different zones—kiddie rides, thrill rides, and VIP

Imagine you’re hosting a party. You’ve got a guest list, but instead of just checking names, you’re also looking at other factors: Are they wearing

Role-Based and Attribute-Based Access: A Beginner’s Guide to Role-Based Access Control (RBAC) Imagine you’re running a busy restaurant. You’ve got chefs in the kitchen, servers

In today’s digital world, building a secure user provisioning process is a critical task for any organization. Whether you’re a small business or a large