
Custom Connector Support in IAM
Imagine you’re building a puzzle, but some of the pieces don’t quite fit. Frustrating, right? Now, think of your organization’s Identity and Access Management (IAM)
Business insights and articles written by our team of world-class professionals

Imagine you’re building a puzzle, but some of the pieces don’t quite fit. Frustrating, right? Now, think of your organization’s Identity and Access Management (IAM)

Let’s face it—managing user access in an organization can feel like herding cats. With so many users, roles, and permissions to keep track of, it’s

Ever feel like managing who gets access to what at work is like playing a never-ending game of “Simon Says”? Traditional access control methods can

Imagine running a ship. You’ve got a crew of talented people, each with their own roles and responsibilities. But what happens when someone new joins
Imagine this: You’re hosting a party, and instead of giving everyone a key to your house, you only hand out keys to the people who
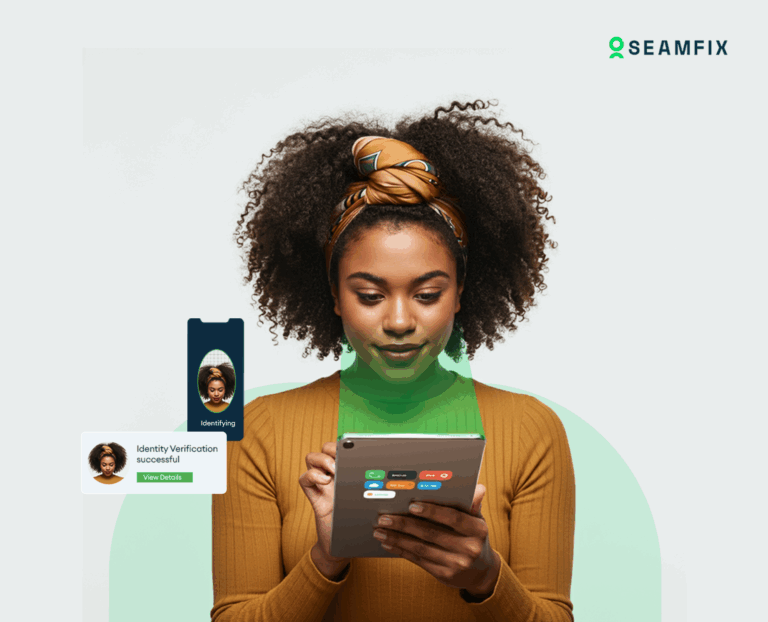
Adaptive Authentication in IAM Let’s talk about security for a minute. We all know it’s important, but let’s be honest—it can also be a hassle.
Imagine you’re handing out keys to your house. You wouldn’t give a spare key to every single person you know, right? Instead, you’d give keys
Role Based vs. Attribute Based vs. Policy Based Access Control Imagine you’re running a theme park. You’ve got different zones—kiddie rides, thrill rides, and VIP

Imagine you’re hosting a party. You’ve got a guest list, but instead of just checking names, you’re also looking at other factors: Are they wearing