Why AI-Powered Image Validation Is a Game Changer for Citizen Enrollment
Why AI-Powered Image Validation Is a Game Changer for Citizen Enrollment Every government wants to make citizen enrollment simple, secure, and fast. But in practice, the smallest things often get in the way. One of the biggest culprits is low-quality photos. Think about it, an applicant submits a blurry passport photo, a selfie taken in […]
Seamfix iAM Just Got More Powerful: 30+ New Integrations to Improve Your Workforce Access Management
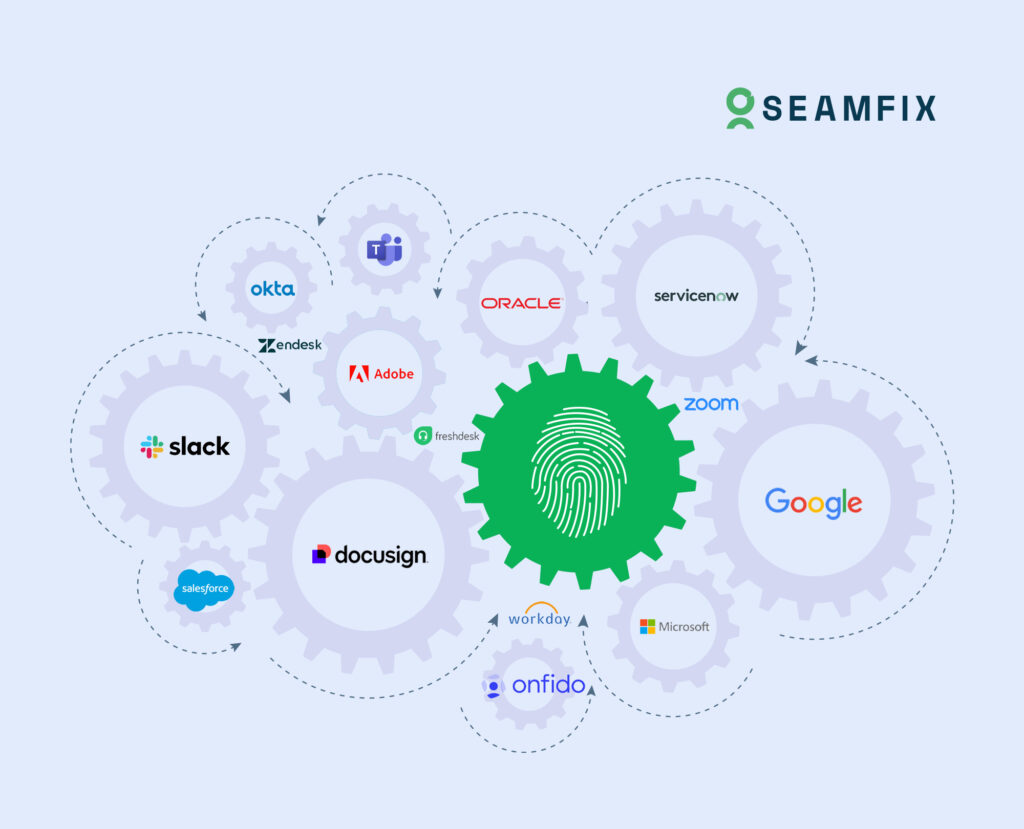
We’ve got some exciting news!! Managing access across different applications is a headache for IT teams, and a serious internal security risk. We know this and that’s why we’ve improved Seamfix iAM with over 30 new integrations, so your identity and access control can keep up with the speed of modern work. Whether your teams […]
Role-Based and Attribute-Based Access in IAM

Role-Based and Attribute-Based Access: A Beginner’s Guide to Role-Based Access Control (RBAC) Imagine you’re running a busy restaurant. You’ve got chefs in the kitchen, servers on the floor, and managers overseeing everything. Now, imagine if the chefs had access to the cash register, or the servers could change the menu. Chaos, right? That’s why you […]
OAuth 2.0: Overview and Use Cases

Ever wondered how you can log into an app using your Google or Facebook account without giving away your password? That’s OAuth 2.0: Overview and Use Cases working its magic! Let’s break it down in plain English—no tech degree required. What is OAuth 2.0? OAuth 2.0 is like a digital bouncer that lets apps access […]
IAM and HIPAA Compliance: Ensuring Data Security

IAM and HIPAA Compliance: Ensuring Data Security in Healthcare When it comes to healthcare, protecting sensitive patient data isn’t just a best practice—it’s the law. The Health Insurance Portability and Accountability Act (HIPAA) sets strict standards for safeguarding patient information, and failing to comply can result in hefty fines and reputational damage. That’s where Identity and Access Management […]
How Hackers Exploit Weak Workforce Identity Systems

James, a payroll manager at a mid-sized company, received an urgent email from his CEO asking him to update payment details for a vendor. The email looked legitimate, even using the CEO’s exact signature. Without questioning it, James made the change. By the time the company realized what had happened, thousands of dollars were already […]
Biometric Authentication: How Secure Is It?

In the world of online security, passwords are so last decade. Let’s face it—they’re annoying to remember, easy to forget, and often not as secure as we’d like. Enter biometric authentication, the futuristic way to log in using your unique physical traits. Think fingerprint scanners, facial recognition, and even voice authentication. It sounds like something […]
Security vs. Privacy: Finding the Right Balance

Internal security is a balancing act. On one side, there’s keeping systems safe from breaches and cyber threats. On the other hand, there’s privacy; protecting enterprise data and ensuring compliance with laws like GDPR and CCPA. These two often clash, leaving you stuck in the middle. The key question is how to find the right […]
How We Helped MTN Côte d’Ivoire Achieve its Objectives

MTN Côte d’Ivoire approached us with a significant operational challenge. As their operations scaled, they were dealing with a surge in capital expenditure as they had to constantly purchase hundreds of new devices for their growing network of agents. If they didn’t do this, SIM activations would be delayed, agents would be frustrated by the […]
The Impact of Security Breaches on Brand Reputation and Customer Trust

“Oh my God! What just happened? How did this get out into the public?” This is usually the reaction when there is a data leak from a security breach. A single security breach can do more than just expose customer data, it destroys the trust they have in your organization and when that trust is […]